This review includes an affiliate link.
In my Beginners Guide to Crypto, I pointed out that a VPN is a necessity for interacting with the full sphere of crypto protocols and activities. There are many reasons why this is the case, in this post I will speak on my personal experience using this VPN over the last years. The links in this post that go to NordVPN are affiliate links. 40% of your subscription will be paid to me if you use these links and sign up. If that bothers you but you still want NordVPN, then sign up later, its not a big deal. If you want to use another VPN, great, use it, again, its not a big deal. I can’t give you my experience about another VPN, because I have not used another VPN for crypto. My review here is my genuine experience and opinion about NordVPN over the past year.
This post is too long for email and will get cut off, please find the entire post on the substack website.
Sign up for NordVPN - My Affiliate Link
Table of Contents
What is a VPN
Ads and information tracking
Why is content region locked
Deeper considerations on VPN usage and privacy
My NordVPN Experience
1. What is a VPN?
A VPN is a Virtual Private Network. To understand how it works, I will explain some basics of the internet, through something you probably understand.
Your street address. The numbers, the city, the state, the zip code. They all associate with a location. If anyone has your street address they can know which legal jurisdiction you belong to and how to find your location. Similarly, the number in your IP address are assigned to you by your ISP (Internet Service Provider) and also includes identifying information. Many internet services like Google, Facebook, etc. will use your IP address to gather information about you, their reasoning for doing so is to serve you with more appropriate ads. You can ask google, and they’ll tell you. Here is my IP address while using NordVPN, this location corresponds with a server farm in Singapore.
You can enter an IP address into this website to see where it is located, which can be of use when checking your VPN.
Depending on the size of a service region, your IP address can tell anyone what city, zip code, or even area code that you live in. I live in a big city, so if I connect to the internet with no VPN, my IP address gives away my zip code, which is a relatively small zip code since I live in the center of a large city (kill me, I know). Anyone with my IP address can already narrow down my location to less than 5 square miles. Your IP address, from a computer, is tied to the router in your home. So if you connect your phone to the WiFi, that device can also be tied to your IP address. I will go more into the consequences of that in Section 2. Your phone has a unique ID tied to it as well, this is called the IMEI (International Mobile Equipment Identity). your cell phone provider, google, microsoft, apple, and the government can triangulate the location of your phone at any given moment from this number alone. Below is a good visualization of just how fine tuned this data tracking can be.
A good VPN program will usually come with a mobile app as well, NordVPN has one and you can protect up to 6 devices with your license. I will admit to not being savvy enough to quite understand how this functionally hides your device, but it is strong enough to completely throw off Google location dependent advertising, however big data companies still know its you, because they recognize the device. In much the same way that when you travel to Peru, you will get ads relevant to your travels but you have not fooled Apple, nor Facebook.
So, to conclude, a VPN is an app or program on your computer that changes your IP address, or changes the location your phone service provider thinks your phone is in. That is one of the basic functions of a VPN, and for an absolute beginner, this is the starting block. The privacy implications I will cover here are interesting, but do not feel overwhelmed and as if you have to do all of this stuff from the start. This substack exists to transmit information to you, and it is your choice how deep you decide to go with that information at any given time.
2. Ads and Information Tracking
So, you now know roughly how large data companies know where you are. But have you ever wondered how these companies seem to craft ads so specific to you that you could almost swear it seems like they are listening in on your conversations? That’s where data analytics comes in, and the implications of what they are doing is far more hair-raising than if they were simply listening in on you, at least for those that tend towards paranoia.
When you log in to facebook, Gmail, connect to any apple service, use youtube while logged in, or just about any other account that requires your phone number, your email, or any other identifying information these companies are constantly trying to tie that information to a “user profile,” and trying to tie that user profile to an address, a place of employment, cell phone, tablet, your Tesla (and any newer car that has GPS enabled). You only have to login once and they will tie your activity together. Google watches all sites you visit, and all search queries you enter, and creates a user profile. For instance, after I wrote the Beginners Guide, Google decided I was probably interested in seeing ads for Crypto hardware wallets based on the things I searched for when organizing the links for that story.
Deeper than that, once a device or vehicle is tied to your user profile, Big Data aggregators will then try to tie other user profiles to you based on how you interact with them. Share the same building at the same times on a regular basis that a business is registered to? Google will assign them a coworker connection in their matrix of user profiles, and if you do extra-curriculars where you share a location often with them but not with a large group of other user profiles that have been deemed “coworkers” Google will assume you are work-friends, and google will suggest ads to you that your work-friend might need to help their job with the hopes that you will bring it up with them in conversation, they pair this with ads sent to your “work-friend” timed so as to coincide with when they presume you will both hang out again. They are right more often than they are wrong. And at times the ads are served near enough to when they predict you will want something that you can often feel as if they have listened to you. This is of course, not true, and you can test this. Choose a random product that you would never buy, write it down, and spend 5 minutes a day talking about it in front of your phone. You’ll never get an ad unless you did a google search for the product you spoke about.
Do you get on facebook and does your Mom say “Happy Birthday, son!” to your account on the same day every year? Facebook now connects your user profiles and will send you ads for things your mothers user profile might want when mothers day and her birthday come near. If both of you entered your cell phone numbers on facebook; then Apple, or Google can now link both of your phones as “mother-son,” and when you go visit and your phone connects to her IP address, or shares the same physical space, you might find yourself getting ads for things she wants, simply because these companies know that you are visiting and might bring it up to your mother. All of this effort is in pursuit of directing consumer spending. Facebook, Google, Apple, and Amazon are very good at this.
Data can be used to connect people into presumed social networks strictly for advertising, and can create user profiles based on other people that do similar things and consume similar items as well. They can create all sorts of obscure, yet functional user profiles. So it makes sense that Google, Facebook, etc. could have no trouble coming up with a list of user profiles that it presumes have crypto, and even further could probably differentiate who has a lot, and who doesn’t. If this information were to be transferred to a government agency at a later point in time, they could most certainly come up with targeted lists of people to audit. The IRS has not come close to this yet, they are choked by bureaucracy and ineptitude. But this is a near-certainty for the future.
Also consider that most people you know will not even opt out of data sharing. Disabuse yourself of any idea you might have about beating the system entirely. Google, Facebook, Amazon, etc. have been building these user profiles since at least 2010 or earlier. You’ve already slipped up. They already know more about you than you probably are aware of. Thats why it seems like the ads are listening to your conversation, they aren’t, they’ve got AI running predictive programming on your user profile compared against millions of other people similar enough to you. No matter how unique or weird you think you are, your Instagram ads probably have pretty good conversion rates on you.
Facebook (through Instagram), has drilled down their predictive programming and their user profiles so much that the ads they serve are extremely niche and unique. No matter what you believe about how unique you are, there are enough people similar to you with similar tastes that have been on the internet or carrying tracking devices for long enough for Instagram ads to be this specific.
You’re not able to escape this, don’t try, I wouldn’t even worry about it. But, now that you know how it works, you can spoof behavior when connected to the internet in normal ways, and then hide all specific behaviors behind a VPN.
Something to consider for the future where an IRS might request user profiles from Facebook, Google, Amazon, Apple or others that these companies consider “crypto users,” is that you can spoof behavior to look like a different type of crypto user in the future. For instance, lets say the IRS knows that you purchased x crypto and had been regularly visiting DeFi platforms. Then one day you spend an hour on google searching and reading articles and forum posts about what to do if you’ve lost access to all of your crypto. Then from that point on you only access DeFi and crypto through one or two dedicated devices with a VPN on always. Well, suddenly your user profile looks like you’ve lost all of your crypto. If you can convincingly hold that story you could probably squeak through an audit in 2026, or limit the amount of resources that the IRS believes you have accumulated.
You can’t overcome the user profile that’s tied to your email address, your cell phone number, and your Identification. But you can intentionally feed them bad information to disrupt their profiling. The quality of information that comes out of an AI, is only as good as the information that goes into it. You win, by feeding bad information to the AI about yourself.
3. Why is Content Region Locked
Many different types of content can be region locked. You’ve probably heard about certain shows and movies being blocked in certain countries due to licensing, copyright, or government policing of content. A most common use of VPN’s is for people to watch shows and movies they otherwise can’t in their country.
During times of political strife, the government will usually enact a partial internet shutdown, where they block access to most sites, but still leave open the ability for communications to occur because they don’t want to disrupt business. A VPN allows you to function normally on the internet during a partial internet shut down. The only way a government can shut down the internet and block a VPN from allowing access would be a total internet shut down within their borders. But to do that, they would have to shut down all communications, including the ones people don’t think about too much like the basic commerce that using a payment card or app allows for. You are ultimately protected from a total internet shutdown due to how dependent governments are on internet financial services to generate revenue and maintain order among the population.
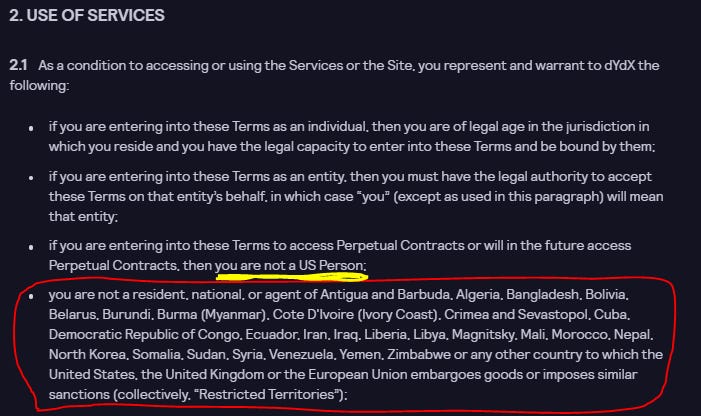
Now, the part of region locking that affects us is typically financial. If you live in the US, you happen to live in a very unique regulatory environment. We are one of the only western countries that has a confiscatory taxing agency that is as well-funded and far reaching as the IRS. Did you know that simply moving to another country and earning all of your income in another country you will still be subjected to paying income tax to the IRS? The only way to escape that is to renounce your US citizenship, and guess what, there is an exit tax you will be charged to do that. You will often find that when reading through the terms of service that restrictions will typically be put on to the US, and for any entity that is under economic sanctions.
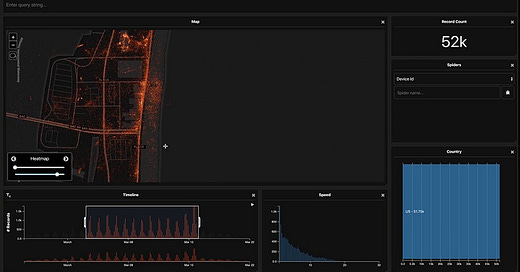
Our access to the financial side of Web 3.0 as Americans is often restricted at similar levels as is the ability of the citizens of Iran, Burundi, and Zimbabwe. However, the US is a large enough market, that often parallel systems will be available specifically for US citizens. This is why Binance has a separate platform explicitly for Americans. The screenshot above is for an on-chain decentralized trading dApp. There is a separate section for Americans that limits leverage, and limits the amount of trade types that you can execute. This country has essentially set up laws that are ostensibly to protect people from being exploited (sarcasm) that only allows users to have access to the full gamut of financial functions once they have a set dollar amount in their account, usually over $50,000. Basically, if you are poor trying to trade, you will get rekt by wealthier people that have more access to the market than you do. As is typical with government, the reason why they tell you they are doing things, is very different from the reasons they are actually doing things.
For instance, take a look at the FINRA regulation for what they call a pattern day trader. They claim its to prevent users from “trading excessively” on margin. But you can only make 4 trades in a 5 day week before you are stopped… unless of course you have over $25,000 in your account. Who exactly does this protect? It protects large brokerages from having users turn their accounts negative during large black swan events. It does not protect the individual trader themselves. But the legislation is phrased as if it is to protect the poor from their own stupidity. Legislation like this is rarer overseas; and due to the relative strength of the IRS, SEC and the US’s ability to sanction and influence other countries to enact sanctions or block services, most dApps and financial services will simply make a token effort to block US customers rather than risk having their web-hosting services through AWS (Amazon) cut off.
This also applies to online gambling. Since these activities are regulated heavily by certain jurisdictions, most online casinos will similarly region block rather than dealing with being targeted by these governments.
The above is a disclaimer from a fully decentralized online casino. A VPN allows you to get around all of these restrictions.
4. Deeper Considerations on VPN Usage and Privacy
So, we’ve outlined how ads are targeted, and the sorts of region locked services a VPN can allow you to use. Now lets take some deeper considerations into privacy and security that a VPN may allow, and what someone who is crypto wealthy might be doing.
First, I want to start with an extreme example of how simply bringing an electronic device with you is often enough for entities to determine where things are. You are not being tracked like this because no one cares about you this much to look deeply into your data. But this is what’s possible. I have often recommended that people going to political rallies, riots, or revolts do not bring their cell phone with them. Even if you are going to what could be a tame rally today, you do not know what a government of the future might consider to be a problematic political group. Even something as simple as going to a movie premiere in 2017 for press freedom, might make you a member of a targeted group in 2035. Notice in the video below how nearly all government buildings that were looked at had no data from inside, because they do not allow cell phones past a certain point.
The data from this simple exercise tracking equipment, similar to a fitbit, even confirmed such conspiracy theorist red meat, like secret military bases in Antarctica.
Now lets pivot away from government conspiracies and instead think about the personal implications. For a fairly insignificant sum on the deep web someone can essentially buy your “user profile.” With something as simple as a name and a phone number, anyone can find your full address on the internet fairly easily. It would be fairly simple for an individual with some decent tech savvy to make an AI to sift through this data and identify which facebook accounts are interacting with crypto, and crypto adjacent content. From there, a simple key-logger or malicious tracking cookie could be sent to all of the email addresses and phone numbers identified. I’m not imaginative enough to be able to conceive of all of the potential ways through which malicious files could be given to you, but here is a recent one called a Zero Click Exploit. To understand that, a One click exploit is something that requires the victim to do something. For instance, if sent a malicious link, all you have to do is not click the link, and you are not at risk. This is a One Click Exploit, it requires one click from a user before it can activate. A Zero Click exploit, is one within which you as the user are completely incapable of doing anything to stop it. If you want to read the linked story about Zero Click Exploits, you certainly can. To save you some time, this is the conclusion.
Apple wanted to make .gifs play automatically when received, so they implemented some auto-executing code whenever someone sends you a .gif in an I-message. So the hacker created a .pdf with a .gif extension that exploits this auto-executing code to then build an entire virus on the device as soon as the .gif is received. That is a Zero-Click Exploit.
And Facebook sold all of the data necessary for a hacker to do that. And no doubt, many other types of Zero Click Exploits exist for the extremely creative and gifted hacker.
So what does a high net worth crypto trader do? They have a dedicated device for crypto only and nothing else. This device never logs in to any platform. No youtube, no gmail, no facebook, no google searches, nothing. This device exclusively uses a VPN. If someone identifies you as a crypto user and tries to target your email or messaging, well the virus will get installed on the wrong device and can’t target your crypto wallets.
Someone will also have a difficult time identifying you as a crypto user in the first place. This is because of something that the SEO and online advertising crowd know well. Lets say you open google chrome and have a tab on youtube where you’re listening to a video about bridges collapsing in China. Afterwards you decide you want to trade crypto, but you leave the youtube tab open. Sure, you turn on your VPN, but google sees that your youtube account has jumped from one IP to another, and they can follow you knowing you are now operating from an IP in Thailand. Any activities you do during this browsing session is tied to your youtube account, and then tied to your larger “user profile.”
The mistake that was made here was that you as a user were not using a clean browsing session, and google was simply able to follow you to your new IP address. In general, we are not perfect, and are often too lazy to clear our browsing history and cookies and then turn our computer off and on again before starting a new browsing session for crypto. We are too forgetful for that. The solution is to have an entirely separate device.
Do you need to be operating at this level of security? No. as I said again, there is simply so much data out there, and you are likely small enough of a user to be protected by the apathy and limited time of an attacker. But if your fortunes grow to the point where you have 7 figures or more of crypto (in 2021 $$ terms) you need to start considering just how much separation you want to put between your money and the internets accessibility to your computer. Some could even make an argument for building their own VPN network. Which is not impossible, but outside of my wheelhouse to explain.
5. My NordVPN experience
Now that I’ve explained just how in depth you can get, lets zoom back out and focus on ourselves. Under 7 figures of crypto, a VPN gives you the ability to access region locked financial protocols within crypto that are of value to you to use. Above 7 figures of crypto, a VPN is a necessity and provides significant security to you as a user.
I’m not above 7 figures, and currently use NordVPN to facilitate my use of crypto on my devices. And I am planning ahead for my own personal security. As stated earlier, NordVPN gives you 6 licenses to use on 6 devices if you choose. The interface is fairly straightforward, both on PC and on mobile.
You can select any country that is on the map and mirror your internet connection through a server in that country. Your internet will of course, slow down (but you can still stream videos and music just fine), you’ll notice the ads you get will presume you are in another country and can change drastically from what you may be used to.
For you to put this into context, a VPN is something you should be considering once you have put a few thousand dollars into crypto. This isn’t something that you need to have in place before you’ve even bought your first crypto. You aren’t making a mistake if your first purchase is from a fully KYCed account you have on a CEx. You can integrate new things as you come to need them. In a few years, you will need to be comfortable using a VPN often, as I suspect the regulatory regime here in the US will tighten their grip on society significantly. But that has not happened yet. Do not let an over-abundance of information paralyze your decision making.
My recommendation? The time to invest in a VPN is after you have taken custody of crypto, and after you have started engaging with dApps and smart contracts. There is a point when your access to a dApp might be paying you more than the cost of the VPN, and its a no brainer at that point.
For pricing, NordVPN is fairly cheap, and there is a christmas deal going currently. Obviously, buying a longer plan is cheaper per month, and is my recommendation. When I purchased my plan, it cost me $96.12 for 2 years, so it’s probable that the "Christmas Deal” isn’t a real deal and is just a sales tactic to push a sense of urgency on visitors to the site, since I paid the exact same as the advertised Christmas deal.
As a side note, one fairly common sales tacticprice, is for retailers to tell you the regular price, and claim the good/service is actually on sale. It’s a pressure tactic to make you feel as if you need to buy right now. There is almost no purchase that is so urgent that you can’t sleep on it, even subscribing to this substack before the paywall goes up on January 16th.
If you feel like you can’t sleep on a purchase, then thats a good sign that you shouldn’t be buying whatever it is you are considering in that exact moment.
Since I bought my plan with NordVPN, I have had zero complaints. I use it for a number of things, primarily interacting with an online blockchain casino whose governance tokens I own a portion of, and interacting with dApps that are region locked, including the governance of an on chain leveraged trading dApp, and for farming Liquidity on a DEx that was region locked as well. I have so far never had an issue where the VPN failed, but I will admit that I am not certain how secure the back-end of NordVPN is. For instance, are they selling my information on the deepweb? I don’t know. Is there a backdoor installed through which a government agency could track my browsing habits? I don’t know. I do not know what I do not know. And I reserve the right to change my opinion in the future if I were to gain new information. And if that new information is relevant I will update this post and let you all know. But so far, my experience with NordVPN has been positive and I feel that for $96.12 across 2 years it has been good value for me. If you are looking for a recommendation, I definitely recommend NordVPN as a place to start.













Will a VPN prevent the future association of two devices that are connected to it- one where you interact as your user profile and one where you never link to your user profile (for crypto)?
Good insight on VPN and all but this >>>"If you feel like you can’t sleep on a purchase, then thats a good sign that you shouldn’t be buying whatever it is you are considering in that exact moment."